This blog post is a follow-up to It’s Time to Ditch Gmail. It began as a review of Fastmail, and my experience of moving to it from Gmail, but I quickly found myself going on a tangent. Since privacy was the main driver in my decision to move to Fastmail, and using a custom domain is one of the ways that I protect my privacy, I figured it was important enough to warrant its own post.
One of the factors that made it easier to move away from Gmail is my use of a custom domain for most of my mail. Before moving to Fastmail, this domain was tied to a GSuite account which forwarded everything to my standard Gmail account. This made switching in anger much easier, as I had fewer accounts to log in to and update my email address, and those that were still pointing directly at Gmail tended to be older low-value accounts that I no longer use anyway.
In this article though, I want to take a detour to explain why I use a custom domain, and how it can aid your privacy.
How does using a personal domain improve your privacy?
Surely the public whois information is actually providing more information, and you stand out more than you would otherwise?
In the case of a human observer, that is true. But unless you’re a public figure or a particularly high-value target, automated machine processing is a far bigger risk. As the BBC recently started requiring users to create and sign in to an account to watch iPlayer online, I’m going to use their statement on sharing your data with other organisations as an example (emphasis is mine):
We use your information to improve your experience. Our service means that we keep your information inside the BBC unless you ask us or give us your permission to share it, for example:
- You ask us to or give us your permission
- To provide you with content and services through a partner’s platform
- If you have a BBC account we might use information that we hold about you to show you relevant and “targeted advertising” through other companies’ sites, like Facebook, Google, Snapchat or Twitter. To do this, we securely match encrypted email addresses with the social media platform via our third party processor, Salesforce. The encrypted email addresses are only decipherable by the social media company if the email address is linked to an account on their site. We don’t provide any new data on BBC users, or their friends. If you don’t want to see our targeted advertising, you can set ad preferences in your social media companies’ settings. You can also visit your BBC account and turn off personalisation, which will turn off all personalised services
Your email address is a common unique identifier that is used to identify you and link your accounts across the web. The BBC creates a hash of your email address, and sends it to Facebook via Salesforce (despite the wording, I’m going to assume this is technically not encryption, as it shouldn’t be reversible). The hashing algorithm is also known to Facebook, and presumably they have a hash table of their user’s email addresses. So if they get a match, Facebook knows you are an iPlayer user, in addition to whatever other information they already hold on you.
For its part, the BBC says it does not provide any new information, so the information leakage is likely small, and (this is purely conjecture on my part), it’s probably only so the BBC can target its own users with ads on Facebook when it desires, or use analytics from the social networks to learn about the demographics of its users. However this type of arrangement is common, and it should be fairly obvious that not all companies will behave as ethically or responsibly with your data as the BBC. Thus if you use the same email address everywhere, you are probably providing Google and the social networks with more information than you intend.
Using a unique address for each site raises a barrier to this kind of tracking. If I sign up to BBC with the email address [email protected], and to Facebook as [email protected], my accounts can not be matched in this way. To Facebook, it looks as though I don’t have an account on their platform, so the advertiser gets nothing.
That sounds like a pain in the arse
Creating a separate account or mailbox for every sign-up would be very time-consuming (and in the case of Fastmail, costly). Fortunately, just about every mail server ever created supports aliases, and one such alias is “*”, also known as a “catch-all” alias. Creating an alias called *@mydomain.com forwards all messages for unknown accounts to a given mailbox.
So if the only mailbox on mydomain is john@mydomain, and I point *@mydomain to john@mydomain; a message sent to jane@mydomain (or anything@mydomain) will be delivered to the mailbox of john.
Problem solved, right? Unfortunately, no. While email address is the low-hanging fruit, there are many other ways to identify you on the web. In particular, your phone number.
When two-factor authentication can harm your privacy
Two-factor authentication (2FA) is absolutely critical to protect accounts of any value. For the uninitiated, 2FA is simply a second method of authentication which is required to log on to an account. Generally speaking, there are 3 major ways it is implemented today:
- The token-based approach, where both you and the account provider know a secret. This secret is used to generate time-based 6-digit tokens, which you send with your password. These can be hardware based (you may have encountered RSA SecureID tokens in your working life), or software based, such as the Google Authenticator app.
- The USB hardware dongle approach, most commonly U2F, or Universal Second Factor, e.g. Yubikey.
- A time-based message sent to you out-of band, e.g. via SMS.
I use all 3 methods, but it’s the SMS method that I have a problem with.
For a start, it’s officially deprecated in the NIST Guidelines, and widely considered to be less secure than the other two methods (although none of them are perfect). The main weakness is SIM-jacking, where social engineering is used to convince a customer support representative from your mobile phone company to port your number to a new SIM. Once that happens, your SMS codes will be sent to the attacker’s phone. This method was implicated in recent bitcoin heists.
But the focus of this article is privacy and not security[1]. By giving up your phone number you are gifting the company a very sticky unique identifier than can be used to track you across the web.
This is why I think offering only SMS as a 2FA solution is a dick move – it forces the user to choose between privacy and security, and there’s no good reason to make this trade-off. And it’s the least-secure method to boot!
I do want to stress though; SMS 2FA is infinitely better than just a password. When it’s the only option I would still use it, assuming I valued the account. If you’re really worried about tracking I’d suggest a dual-sim smartphone and a second number which is not known to social media companies, credit agencies or data brokers, but otherwise just use a strong unique password.
Improvement Required
Facebook and Google have always had excellent options for two-factor authentication, and I’d go so far as to say they have led the way in offering 2FA to the general internet population. This makes sense, as they are large companies and their accounts are highly valued and often central to their owner’s digital lives. But some companies limit your options.
The most egregious example, until recently, was Twitter. For a long time, SMS codes were the only supported 2FA method, but I now see they have added both U2F and mobile security apps (you can activate them here).
One holdout I’d like to call out though is Paypal. They were initially ahead of the curve, and offered the option to order hardware security tokens long before OTP apps became common-place. There was a price for the hardware tokens, but it was reasonable, and they later added support for the Symantec VIP Access app, which was free.
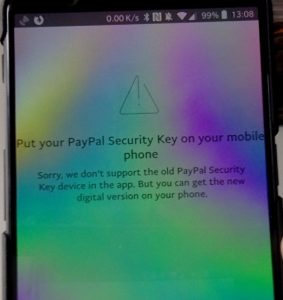
Unfortunately, they’re now way behind because the PayPal Android app does not support anything but SMS. When I try to login with the PayPal app with non-SMS 2FA enabled, I get the following message:
The “new digital version” referenced is actually just SMS codes, which is a big step backwards from the hardware tokens they used to issue, and the supported Symantec VIP Access app. It doesn’t make sense, and really isn’t good enough in 2018[2].
Spam Glorious Spam
Spam is much less of a problem these days, as email is increasingly concentrated in large entities such as Google and Microsoft, who have vast amounts of data with which to train their anti-spam algorithms. That said, if you do start getting spam, a unique email address could tell you who leaked or sold your information.
Also, if you do have trouble it gives you a nuclear option for blocking spam – simply add a rule which immediately deletes all mail sent to the receiving address. No more Bayesian filters!
Security through obscurity
A lot of account compromises come from “credential stuffing”, which is essentially trying leaked username/password combinations from one site on another.
Say I create an account at Amazon with my personal email address, and do the same on eBay. I can’t be bothered to remember multiple passwords, so I use the same password on both sites with no 2FA. Amazon is then hacked, we find out that they didn’t secure their passwords very well, and my email address and password combination is leaked in plain text. Now, hackers have a unique username and password combination which they can try on sites all across the web. If they happened to try my Amazon username and password on eBay, they’d get a hit.
Using unique email addresses provides a little (and I do mean little) protection from the above situation – the sin of password reuse. If the email addresses were different in the example above, automated bots would not get a hit unless they did something a bit smarter, like substituting amazon for eBay in the email address (which is probably a waste of time, as anyone savvy enough to use unique email addresses across sites is highly likely to use unique passwords as well).
Arguably, a common password, combined with two-factor authentication and a unique email addresses wold be an acceptable level of risk for low-value accounts that contain little to no personal data. But in the interests of forming a healthy habit with your password manager I’d strongly discourage it.
Limitations
A custom domain is no panacea for protecting privacy, but combined with unique addresses it raises the bar significantly when it comes to automatically tracking you across the web. It’s important to lay out the caveats though.
- Email address is only one piece of data that can identify you. Phone number is another, and while it’s easiest to track you with unique identifiers such as email and phone, statistical modelling and combinations of other data (name, birthday, cookies, web browser fingerprint, IP address) can all be combined to track you with a high degree of confidence. The less information you give up, the harder it will be to track you.
- Many companies, particularly social media networks, will remember every piece of information you give them forever, so even if you remove an email address or phone number from your account, there’s nothing to stop them matching on it anyway. I suspect they would match you until another user registered it against a different account. So don’t remove your email from Facebook, then assume you can use it on other sites without them tracking you.
- If you browse while signed in to Facebook, Google, or any social media site, all this is moot and it’s game over for your privacy anyway. You have their cookies in your web browser, so any site that includes their social buttons or ad network cookies will immediately link your visit to your social media profile.
- With a custom domain, the registrar becomes another link in the security chain that is critical to secure. Any reputable registrar will support 2FA and good security practice for securing your account, but it is a risk to be aware of.
Other tips
- Don’t give up your phone number unless you absolutely have to. It’s an even stronger unique identifier than your email address, because people rarely change their mobile number and are more likely to have only one of them. It’s also much harder to get ephemeral phone numbers.
- Don’t sign in to Google or any social media profile on any web browser that you use for searching or browsing the web.
- Use separate web browser profiles for social media, shopping, and general browsing. Chrome’s browser profile implementation is the most polished, but I place a lot more trust in Firefox.
Conclusion
I’ve deliberately skirted security in this article to keep it short. Yes you should use 2FA, a password manager, and strong, unique passwords.
But these do nothing to protect you from tracking across the internet, which is both ubiquitous and sophisticated. Taking control of your data is hard, and it’s easy to leak information unless you constantly keep your guard up. For all I know, accidentally signing in to a social media account in my shopping browser profile could immediately link my entire purchase history to that account. There’s a whole network of shady data-brokers out there that are hoovering up all the personal data they can, and it only takes a single lapse for them to get data that you didn’t intend.
So if you don’t already have your own domain, I’d strongly recommend that you get one. Not only is it more professional, but when you use unique addresses it makes tracking you that little bit harder.
And of course the original reason I went off on this tangent (which I mention for the first time in the conclusion); using your own domain decouples your email address from your email provider.
This makes switching provider easier. Just as Gmail and Hotmail liberated us from ISP email accounts and allowed us to keep an email address for life (anyone in New Zealand still rocking an @xtra.co.nz email address?), Using your own domain allows you to move your email to a new service without changing address.
I hope that was useful. People sometimes look at me like I’m a bit mad when I talk about using unique accounts for email and separate web browser profiles for different tasks, but there’s a very good reason behind it all: data.
-
- [1] For the record, I don’t think using a custom domain offers any security benefit. If anything it introduces additional risk. Assuming you can secure your domain registrar account, and trust your registrar not to succumb to social engineering, I think the benefits outweigh the risks.
- [2] Not sure I really need to mention this when I’m criticising them, but in the interests of full disclosure, I have a small financial interest in Paypal.